Using IP based storage in conjunction with 2 pNIC Transport Nodes makes traffic engineering inevitable.
Most servers nowadays are equipped with only 2 physical 10 Gb NICs. As NSX-T comes with its own virtual switch – the N-VDS – we have to connect our VMkernel Adapters to the N-VDS to preserve uplink redundancy as a single pNIC can belong to just one virtual switch.
In vSphere we can configure active/standby/unused uplinks per port group to bind traffic types like vMotion, Management or vSAN to specific uplinks. For example: we run vMotion traffic per default on vmnic0, use vmnic1 as standby and configure vSAN vice-versa. But how can we create the same setup when we have to use Segments (aka Logical Switches) in NSX-T.
In this post I will show what needs to be done to connect an ESXi host to a iSCSI storage array. If you are not familiar with configuring iSCSI based storage and its requirements in vSphere, please take a look here:
Intended Result
- 2 VLAN based Segments for iSCSI use
- First segment: iSCSI1 forwarding traffic only via uplink-1
- Second segment: iSCSI2 forwarding traffice only via uplink-2
My ESXi hosts are already configured and connected to NSX-T, meaning both vmnics are attached to an N-VDS using a default teaming policy of Load balance source.
Edit Uplink Profile
First we have to edit the Uplink Profile that is attached to our ESXi Transport Nodes; we need to add 2 new (custom) Teamings. In my example I have a default teaming using “Load balance source” with both uplinks active. Now lets add two teamings with only one active uplink and a teaming policy of “Failover Order”.
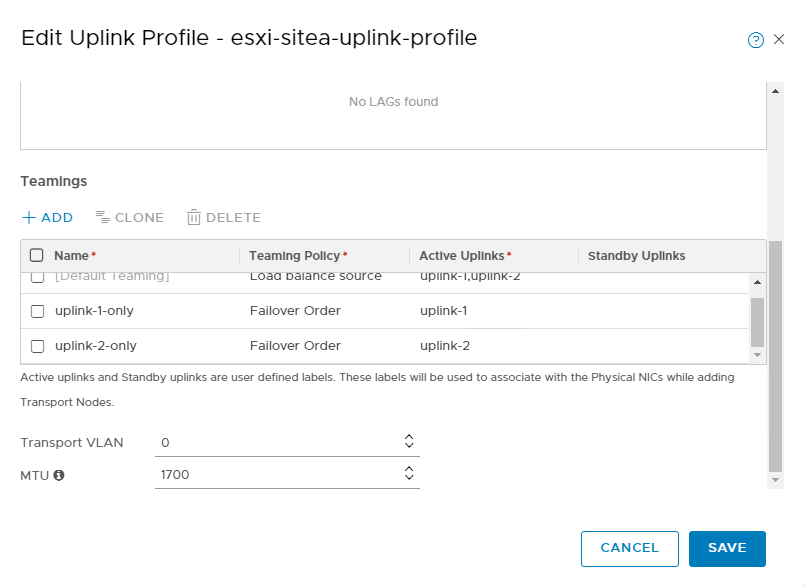
In the screenshot above you can see the additional Teamings. You can see that both of them have only one active uplink.
Hint: from my own experience I can recommend to check twice for typos… 😉
Change Transport Zone
Now comes a step that is overseen very easily: We need to register the new Teamings with our Transport Zone:
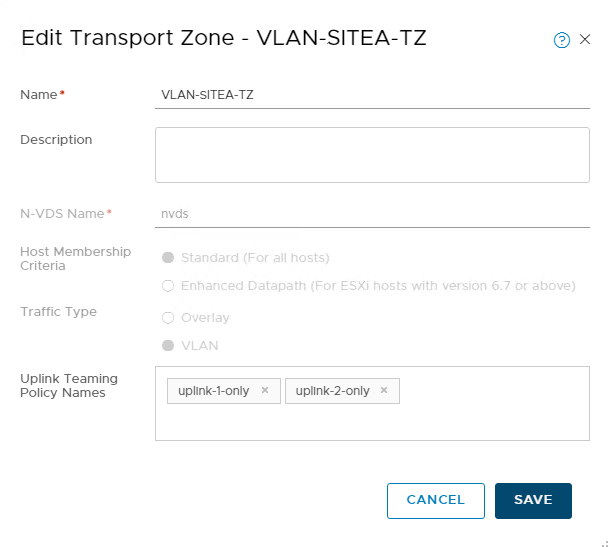
You have to add the names of the new teaming policies to the corresponding field as shown in the screenshot above.
Create Segments
Finally we can create our iSCSI Segments, which is a two-step process:
- Create the Segment and make sure it is part of the VLAN TZ that has the teaming policies added. Click SAVE and then click NO on the question: “Want to continue configuring this Segment”. Then wait for the Segment to be “Up”
- Next expand the new Segment and click Advanced Configuration.

This will send you to the Switches view in the Advanced UI. Click Edit on the Overview tab of your new created Segment/Switch. Now you are able to change the Teaming Policy:
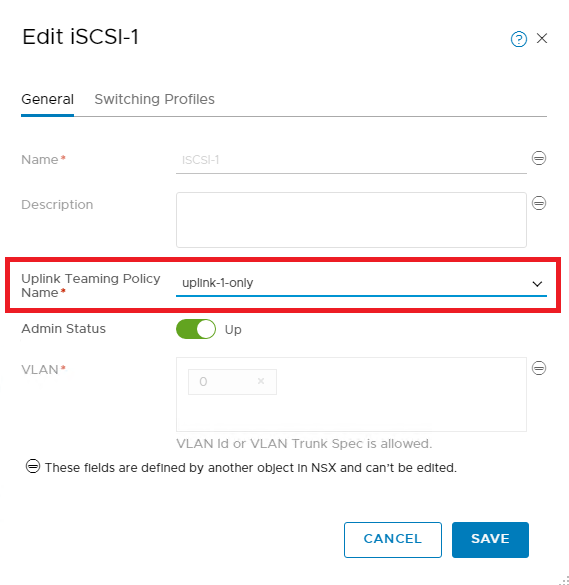
Repeat the steps above to create a second Segment that uses only uplink-2 and you are ready to configure your iSCSI VMkernel Adapters and the Network Bindings.
In this example I created a Segment for iSCSI use that requires only one uplink to be active. If you want to have Segment with a active and a standby uplink – for example for vMotion – you just have to add the second uplink to the “Standby Uplinks” column in the Uplink Profile.
Whats Next…
In one of my upcoming posts I want to discuss how to use Transport Node Profiles to prepare ESXi hosts for the use with NSX and migrate all the existing VMkernel Adapters to NSX-T Segments in one step.