Overview :
VMware in EMEA have put together specialist teams for internal product and integration support in the complex EUC arena. These teams are called P.A.C.T. (Product Area Champion Team). As part of this initiative the VMware Identity Manager Product Area Champion Team as a start have also wanted to foster help on getting one started.
One of the Team members Stavros Charalambous has worked out a fantastic way to build his own EUC SAAS lab. He kindly worked with me as the author of this document to build my own 100% EUC SAAS lab. Whilst building my lab we documented the steps. We are hoping this will encourage more in the EUC community to play with VMware technologies and with a view to fostering confidence when working with VMware diverse product stack
As the lab is 100% SAAS, there are several advantages some being that one does not have to worry about all the issues about having your own on premise lab for example, electricity costs, space, noise and unnecessary time wasted on things like split DNS, hardware, capacity. etc
We have to be 100% clear that this has been put together here has to be followed circumspectly. Once this SAAS platform is in place it would give the individual the ability to expand their knowledge round the integration of VMware Identity Manager , WorkspaceONE UEM and SAAS solution out there. We are planning on follow up articles to this where we cover the integrations of Office 365, OKTA PING and also possibly leveraging platforms other than Azure for example Amazon Web Services.
Revisions of this document will be made as we learn and gain experience, we are hoping that by sharing this information it will contribute to a spirit of Collaboration and sharing.
We also intend writing follow-on articles to this document.
Audience:
The primary audience the document is focussing are VMware Internal SE and PSO and VMware Partners. We however realize that a very broad audience could benefit from pieces or the entire document and therefore we are making this publicly available
High level overview of the deployment.
1 . Obtain access to get an MSDN Platforms subscription
- This involves obtaining an Azure subscription and building what could be the equivalent of a physical / on prem in the cloud
- Build an Active directory Domain Controller
- An AirWatch Cloud Connector
- A VMware Identity Manager Connector
- Linux Virtual Machine (Tunnel Server/proxy) centos OS
- Build an Active directory Domain Controller
- Azure DNS Zone
- WordPress
- Custom Domain
2 . Acquire a SAAS VMware Identity Manager Tenant
3 . Acquire a Workspace ONE UEM SAAS Tenant
Signing up and configuring your SAAS Azure Subscription.
1 . Login into your approved MSDN subscriptions with your VMware account , username and password
2 . Activate your Azure $100 Monthly credit subscription, select Activate

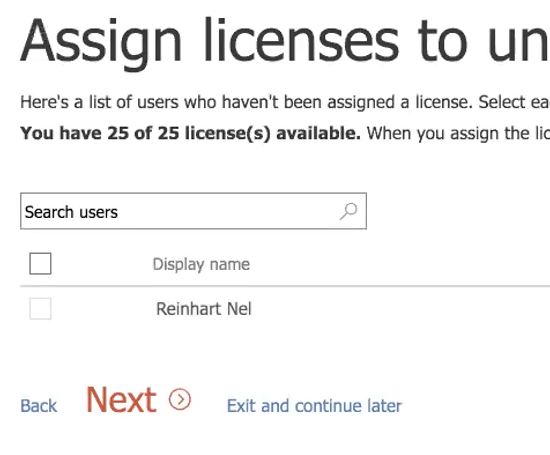
3 . On the Microsoft Pick an account page select your MSDN platform subscription account

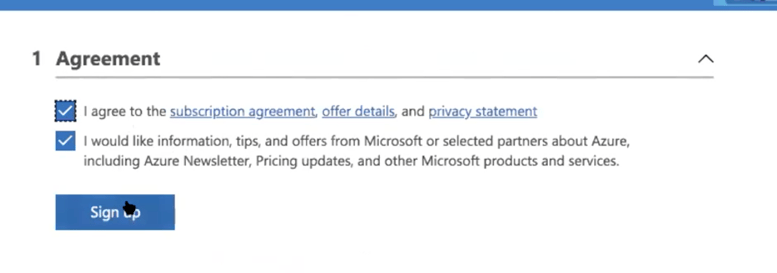
4 . On the Agreement window, select the I agree to … checkbox and select Sign Up
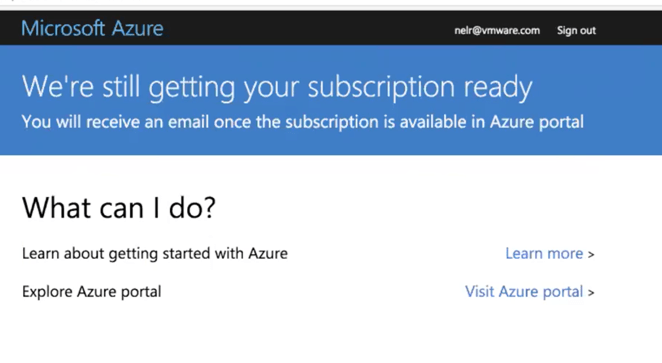
5 . On the We’re still getting your subscription ready, select Visit Azure Portal
6 . Close the You have free Azure recommendations window

7 . Select Maybe later on the Welcome to Microsoft Azure window

8 . At the top of the Window select Notifications

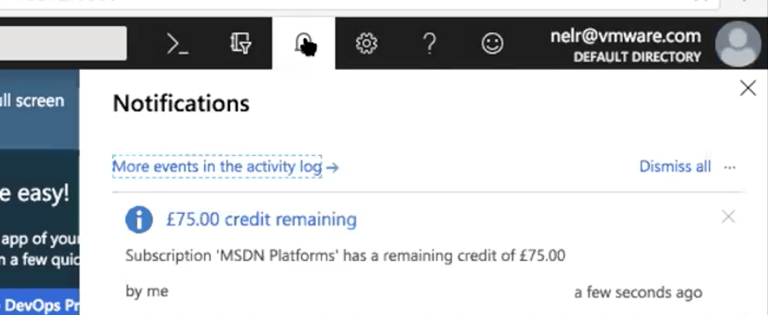
Notice your remaining MSDN subscription Credit (this might vary from subscription to subscription)
9 . To the left of the window select Virtual Machines


10 . At the top of the Virtual Machines windows select ADD
11 . To the right under Recommended select Windows Server

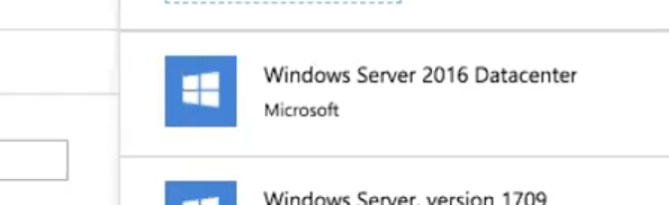
12 . To the right select Windows server 2016 Datacenter
13 . Leave the default Under Select a deployment model and select Create
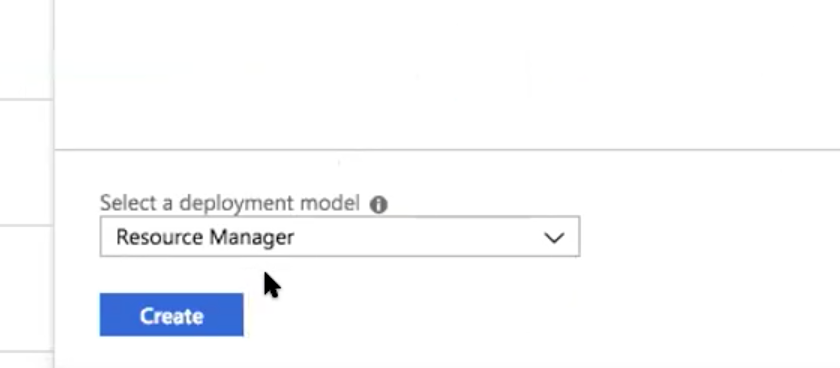
14 . Under the Basics Area Type in the following information
- Name
- UserName
- Password
- select Create New radio button and then type a Name, select your location,
- Under Already have a Windows License? select Yes

- Under license type , select the check box to confirm your eligibility and select OK

15 . Under the Available section select the 3rd option which offers one 2 vCPU’s and 4GB of RAM and click on Select

16 . Step 3 Settings
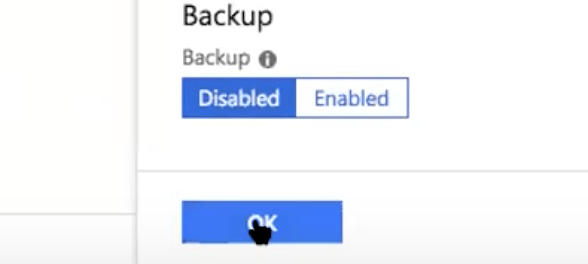
In the Settings Window Select Availability Set > Select + Create new, In the Name section type a name and then select OK

17 . Back to the settings page, scroll down to Auto-shutdown and ensure Off is selected


18 . In the Settings interface under the Select public inbound ports select the RDP (3389) checkbox
19 . Select OK right on the bottom of the Settings window
20 . On Step 4 On the bottom of the Create window select the I give Microsoft…. Check box and select Create


21 . Create a Linux virtual machine
a. In the Azure Admin Console select Virtual Machines, then select ADD

b. On the Compute page select the CentOS-based 7.3 virtual machine

c To the right of the Compute window under CentOS-based 7.3 select Create

d. Under Basics type in the following :
- Under Name : Type TUNNEL
- Under Username: enter your ADMIN username and Password
- Under Resource group select your existing “Resource group”
- Under Location: select your Location
- Select OK


e. On the Choose size page, select 1 vCPU and 2 GB of RAM click on Select
f. On the Settings window select Availability set and to the right select your “Availability Set”

g. Under Select public inbound ports select SSH (22)
h. Disable Auto-Shutdown by selecting Off


i. Select OK
j. On the Summary page Accept the Terms of Use by selecting the checkbox and select Create

22 . Create a Load Balancer
To the left of the Azure Admin Payne select Load balancers

23 . Under Load balancers select + ADD

24 . In the Create Load balancer Fill in the following
a . Next to Name type in a name
b. Under Public IP Address, select Create New radio button

c. Under Assignment: Select Static radio button

d. Under Resource Group
e. Select Create New Radio radio button and type in a Name like Reinhart_Lab

f. Under Location e.g. If you live in the UK select Western Europe
g. Select Create
25 . Once the Load-balancer has been created select LB

26 . Under Load balancer configuration options select Inbound NAT rules


27 . To right select +ADD
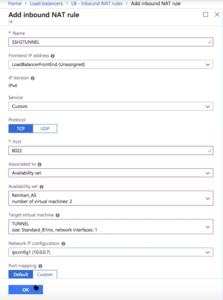
28 . On the Add inbound NAT rule window, add the following
- Under Name: type SSHTUNNEL
- Under Front end IPADDRESS : Leave unassigned
- Under Port type: 8022
- Under Associated to select Availability set
- Under Availability Set select your “custom Availability Set”

- Under Target Virtual machine, select your TUNNEL server

- Under Network IP Configuration select the IPCONFIG interface

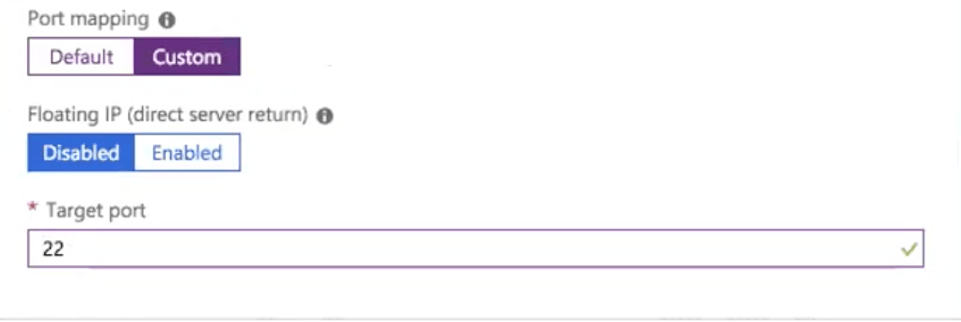
- Under Port Mapping select Custom then under Target port type in port 22

- Review all your settings and then select OK
Testing the configuration
1 . On the Azure Admin Console, select Load balancers

2 . On the Load-balancers Interface, select Overview and copy the Public IP address


3 . Open the Putty if you are on windows and Terminal if you are on a MAC
Here is an example ssh [email protected] -p 8022
When prompted for a password, use your admin password
And type the following if you are on a MAC

4 . Type cat /proc/cpuinfo | more

5 . Type free
6 . Back to the Azure Admin Console, select Virtual Machines > TUNNEL > Public IP

7 . On the TUNNEL-ip window select Dissociate

8 . When prompted select Yes
9 . Wait for a few minutes to update

10 . On the TUNNEL server select Restart to remove the Public IP address from the Console.

11 . On the Azure Admin Console, select Load balancers. On the Load balancers window, select +Add

12 . On the Add inbound NAT rule
a. Under Name type RDP2AD

b. Under Service, ensure that Custom is selected.
c. Under Port type 43389

d. Under Target Virtual Machine select AD

e. Under Network Ip configuration, select ipconfig (whateverIP)

13 . Open up Terminal if you are on a Mac
Here is a Mac example of what one could look like telnet 13.80.249.105 8022
14 . Another way to test this is to open up an RDP client and type the following
Computer Name (use your own Public IP)
Port 43899

WorkspaceONE UEM environment
Overview:
Within VMware we more than one internal publicly available WorkspaceONE UEM environments
My friend Stavros, for example, has access to CN-137 which is a dev environment that requires your manager approval if you get access, this can be sent to [email protected]
Alternatively one can register for a trial on the following link https://www.vmware.com/products/workspace-one/unified-endpoint-management.html
One gets access to SAAS instance of WorkspaceONE UEM and a VMware Identity manager
Once you access to a SAAS instance of WorkspaceONE UEM and VMware Identity Manager, proceed with the following:-
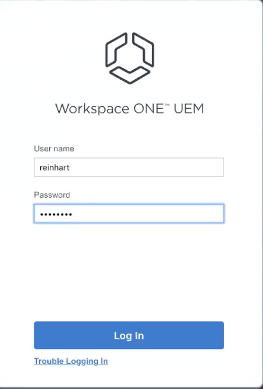
1 . Log in to Workspace ONE UEM with your User Name and Password
2 . On the Terms of Use page select ACCEPT


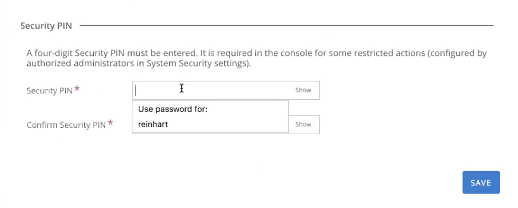
3 . On the Security Settings Page answer the following Password Recovery Questions and type and confirm a Security PIN select SAVE

4 . Close the Workspace ONE UEM Console Highlights page

Configuring Your Active Directory Server in your MSDN
Azure Platform
Overview. We have already deployed a Windows Server in Azure, we will start off by configuring this server with Active Directory Services
1 . Log in to your Azure admin Console with your subscription credentials and select Virtual Machines, then select AD next select the Overview section.
- If you have not done so already, copy the Public IP Address and configure your RDP client with this IP address. Recall we are using port 43389
through the Load-balancer.



2 . Using your RDP client Log in to your AD server with your Admin credentials
3 . Open Server Manager and select Manage, select Add Roles and Features, on the Before you begin wizard select Next

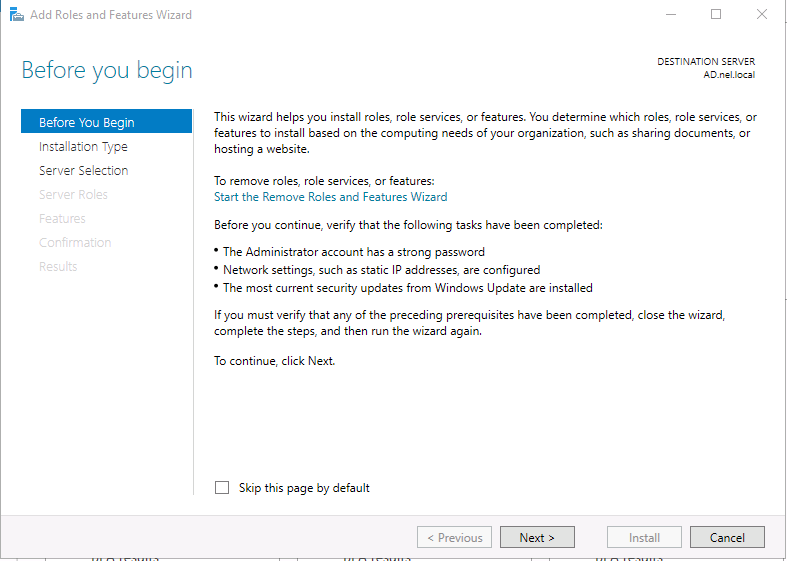
4 . On the Select the installation type window select the Role-based or feature-based installation and select Next

5 . On the Select server roles interface select Active Directory Domain Services checkbox, when the Add Roles and Features Wizard window launches
select the Add Features button


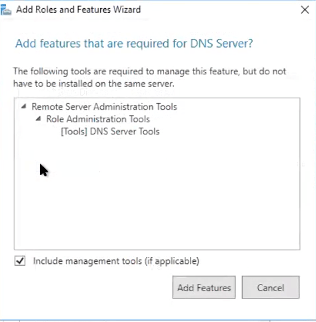
6 . On the Select server roles wizard select the DNS Server checkbox , select Next on the Add Roles and Features Wizard select Add Features, on the Validation Results page select Continue


7 . Back to the Select server roles wizard select Next

8 . On the Select features page select Next

9 . On the Active Directory Domain Services page, select Next

10 . On the DNS Server page select Next

11 . On the Confirm installation selections page select the Restart destination server automatically if required checkbox, when prompted If a restart is
required … window select Yes and then select Install


12 . Select Close

13 . Your AD server will restart and you will lose your RDP session when the AD server has restarted reconnect using your RDP session
14 . The Server Manager console should re-launch, Next to Manage, look for the yellow warning triangle

15 . Select the yellow Triangle and select Promote this server to a domain controller


16 . When the Deployment Configuration wizard launches select the Add a new forest radio button, next to Root domain name: type an internal AD
domain name, for example, nel.local and select Next
17 . On the Domain Controller Options page type in a Directory Services Restore Mode password and confirm and select Next

18 . On DNS Options select Next

19 . On the Additional Options next to The Netbios domain name: box type your netbios name for example Nel and select Next

20 . Accept the default on the Paths window and select Next

21 . On the Review Options select Next

22 . On the Prerequisites Check, ignore the results and select Install

23 . After the reboot reconnect using your RDP client
24 . Go to your Administrative Tools and launch Active Directory Users and Computers


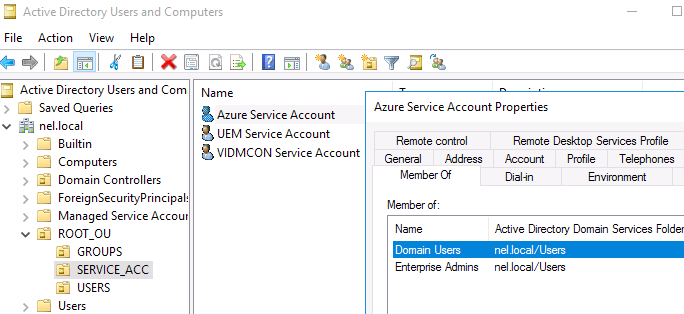
25 . In your Domain Create your own OU structure for USERS, Service_ACC and Groups

26 . In the SERVICE_ACC OU create the following service accounts
- Azure Service Account (Needs to be a member of the Enterprise Admins group)
- UEM Service Account (domain users only)
- VIDMCON Service Account ( domain users only)
Note! ensure that passwords are set to never expire when creating these accounts
27 . In the Users OU under ROOT_OU, create your own test Domain User account

28 . We will deploy a web app to register a publicly resolvable domain name
Go back to your Microsoft Azure Admin Console and select App Services
In the App Services area select +Add

29 . To the right select Web App Microsoft
30 . To the right in the Web App Microsoft select Create

31 . On the Web App Create name
- Under App name Type your name eg Reinhart
- Under Resource Group accept the default and select Create
- Notice validation is successful at the bottom and to the right is Deployment in progress…
- When you see the Deployment succeeded message select Go to resource



32 . In the Microsoft Azure Admin Console select App Services

33 . In the App Services interface select your name with your mouse and open the hyperlink to the name

34 . To the bottom of ”your name App Service” under Settings select Custom domains

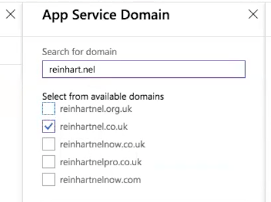
35 . To the right under App Service Domains select + Buy Domain

36 . In the App Service Domain page under Search for domain type a “domain that you would like to use” in your lab environment. Below the Search for
domain section a suggested list of available domains will show. Select your preferred domain name checkbox
37 . To the right under Contact information type in all the REQUIRED information

38 . To the left under App Service Domain select the @(Root domain) checkbox
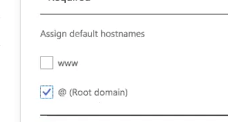
39 . Select Ok to close Contact Information page
40 . In the App Service Domain select *Legal Terms Required, to the right notice the Pricing details page shows, select Accept to close the Pricing details
page.

41 . Select Ok to close the App Service Domain window, to the right you should notice notifications regarding your new domain registration

42 . At the top of the Azure Admin Console select Notifications and read the following events

43 . Wait about 5 minutes and then from the Microsoft Azure Admin Console select All services
44 . Under All services, Scroll down to the bottom left of the Admin Console and select DNS zones
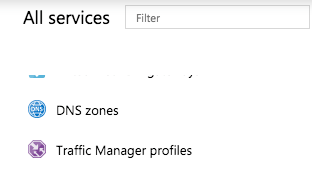
45 . Notice in the DNS zones page under names, notice that your DNS Zone is registered

.
46 . Select your registered DNS Zone to go to its properties

47 . IN YOUR registered DNS Zone properties, in the middle pane, select +Record Set

48 . Fill in the following in the Add record set window
- Under Name type @
- Under IP Address type the external Public facing IP ADDRESS of your Load balancer
- Change the TTL unit from Hours to Minutes

49 . Select OK

50 . Under Name select the first @ line A type
Notice that in your record set your suffix is @.your namespace
Close the window when you’re done

.
51 . Revert back to your RDP AD server session. Go to Administrative Tools > Active Directory Domains and Trusts

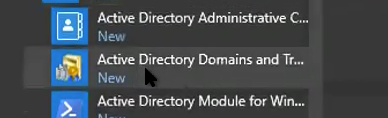
52 . Right click Active Directory Domains and Trusts and select Properties

53 . In the UPN Suffixes window under the Alternative UPN suffixes type your registered domain e.g. reinhartnel.co.uk and select Add

54 . Go back to Active Directory Users and Computers and go to your custom test user in your USERS OU under your ROOT_OU

55 . Select and right click your Test User and go to Properties

56 . In your Test user properties select the Accounts tab, under User logon name: next to your user name change the old suffix to the newly created suffix

57 . Select the General tab and go down to E-mail. Create an email address with the suffix of your registered domain in Azure. e.g. [email protected]

58 . Select OK to close the Test User Properties
Deploying the WorkspaceONE UEM Cloud Connector
1 . Use your RDP Client and connect to your AD server
2 . Open your Internet Explorer browser and type in the URL of your registered SAAS WorkspaceONE UEM tenant allocated to you
3 . Log in to your WorkspaceONE UEM admin Console with your WorkspaceONE UEM admin account

4 . In the WorkspaceONE UEM admin Console select GROUPS & SETTINGS

5 . Under Groups & Settings select All Settings

6 . Under System select Enterprise Integration

7 . Under Enterprise Integration select Cloud Connector
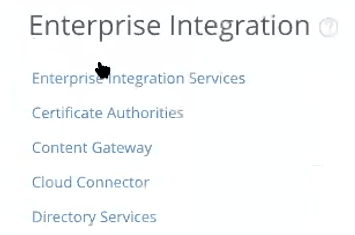
8 . Under Cloud Connector select Download AirWatch Cloud Connector Installer

9 . In the Download ACC-Installer.exe window, type your Workspace ONE UEM admin password and confirm and select DOWNLOAD, when prompted do you want to save select Save

10 . When the download is complete you will be prompted to Run, select Run
11 . On the AirWatch Cloud Connector – Installation Wizard select Next

12 . On the License Agreement window, select the I accept the terms in the license agreement radio button and select Next

13 . On the Destination Folder window select Next
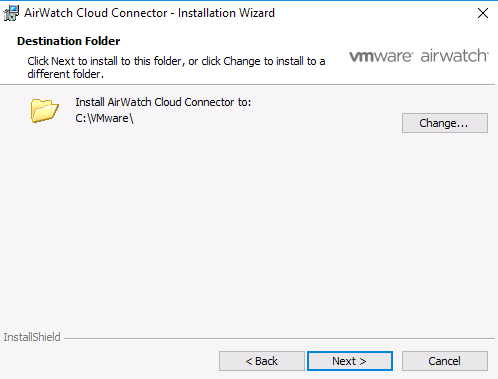
14 . On Proxy Information page , accept the defaults and select Next

15 . On the Ready to Install the Program select Install

16 . When the Installer Wizard Completed windows shows select Finish
17 . Revert back to your Settings > Cloud Connector Page and select TEST CONNECTION

18 . In the Left Inventory under System > Enterprise Integration > select Directory Services

19 . In the Directory Services window next to Current Setting select the Override radio button

20 . On the Directory Services page select CONFIGURE

21 . When prompted Are you going to be using SAML Authentication, select NO
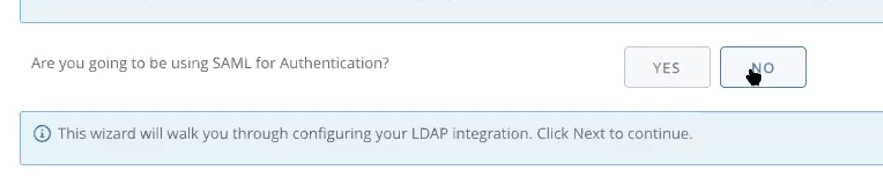
22 . Select NEXT
23 . On the Directory Services Configuration page enter the following :
- Next to Server type the FQDN of your Domain Controller, for example AD.Nel.local
- Next to Authentication User Name type your UEM service account username domain\username
- Next to Authentication Password type your UEM service account password
- Select Next


24 . On the Server Settings page select TEST CONNECTION

25 . On the Users & Groups Settings next to I want to automatically sync the enabled/disabled status of a user, select YES

26 . Select NEXT
27 . On the Directory Setup Complete page next to I would like to enable Directory Services as a method of authentication for enrollment, select YES

28 . Select FINISH
29 . On the next page select Close
30 . Close the Directory Services window
31 . On the WorkspaceOne UEM Admin Console select ACCOUNTS > under Users select List View select ADD > Add User
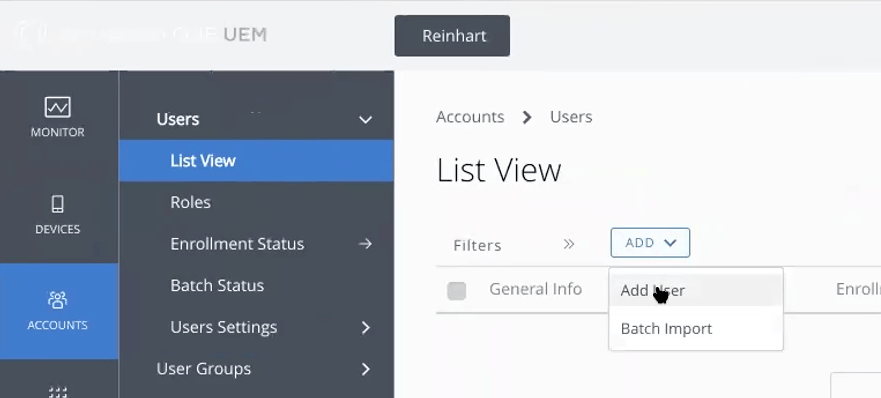
32 . In the Add/Edit User add the following
- Next Security type select DIRECTORY
- Next to User Name in the dropdown select your test user
- Select CHECK USER , notice a few new default properties show up
- Select SAVE




33 . On Settings > Devices & Users > Android > Android EMM Registration Select REGISTER WITH GOOGLE

34 . On the Google Play, Bring Android to Work page, select Get started
35 . On the Business name page under Business name Your answer type your organization name and select Next

36 . On the security of your data within our services page under Data Protection Officer, type in your credentials using a Google Account (preferably dedicated for EMM) agree to the terms and conditions by selecting the checkbox and select Confirm

37 . On the Set up complete page select Complete Registration

Setting UP OFFICE 365 for your online EUC SAAS LAB
Overview.
One needs to set up an Office 365 E3 Developer subscription Account to be able to integrate with Workspace ONE. In this section, we will cover the process of setting this up. Setting up a developer subscription allows you a 12-month free trial. $99 per year thereafter.
1 . Open a browser and go to Google Chrome search engine and type office 365 e3 developer subscription.

2 . Find the option that says Set up an Office 365 developer subscription and select

3 . On the Set up an Office 365 developer subscription page under Set up your subscription Under! Note
Select the join the Office 365 Developer Program hyperlink

4 . On the Welcome to the Office 365 Developer Program page select the Join the Office 365 Developer Program page

5 . You will now be re-directed a 3rd time to the Join the Office 365 developer program today! Do not select JOIN NOW
6 . To the right of the page select Sign In

7 . On Microsoft Sign in Page type in the email address of an account you own

8 . On the Welcome to the Office 365 Developer Program! Page under Country / Region select your country and type the name of your Company, select the I accept the Terms… and I would like to hear…. Checkboxes and then select Next
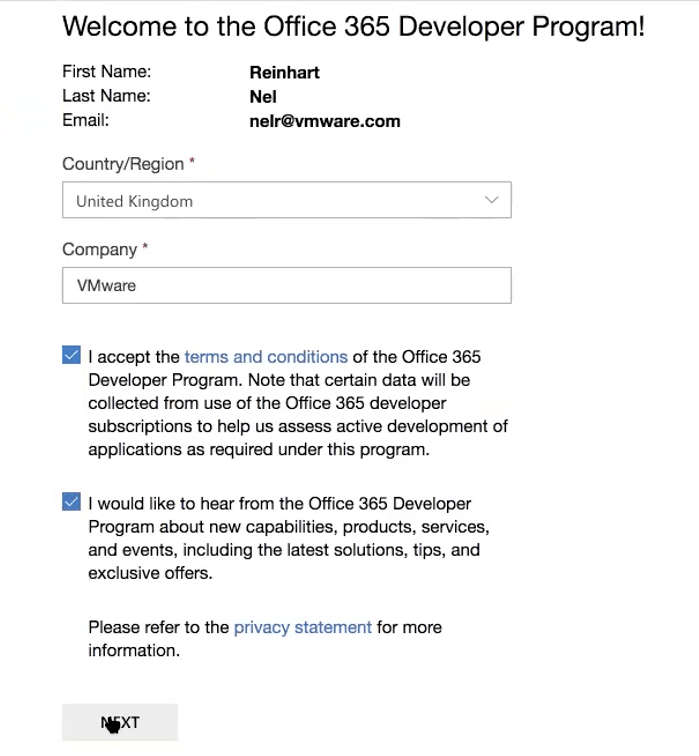
9 . On the Office 365 Developer Program Preferences page select enough checkbox and options to make sure the Join button becomes available and the select JOIN


10 . Close the Welcome to the Office 365 Developer Program! Window

11 . On the Office 365 Developer Page select SET UP SUBSCRIPTION

12 . In the Setup your developer subscription window, create a unique admin account, for example, your username could be CloudAdmin and your Domain could be your firstname and surname
NB! Ensure you document these credentials
- When you are done select Continue
- On the Add phone number for security window type in your Country Code and your phone number
Select SEND code, Enter the Code from your phone and select Set up

13 . Once your registration is complete you can login in using your new ADMIN account. On the Your Office 365 Subscription page select the office.com hyperlink

14 . On the Sign In window, Enter your password and select Sign in

15 . On the Office 365 Page almost in the middle select Admin
16 . On the sign in page pick your new CloudAdmin account

17 . On the Welcome to Office 365 Admin Center Page select Skip

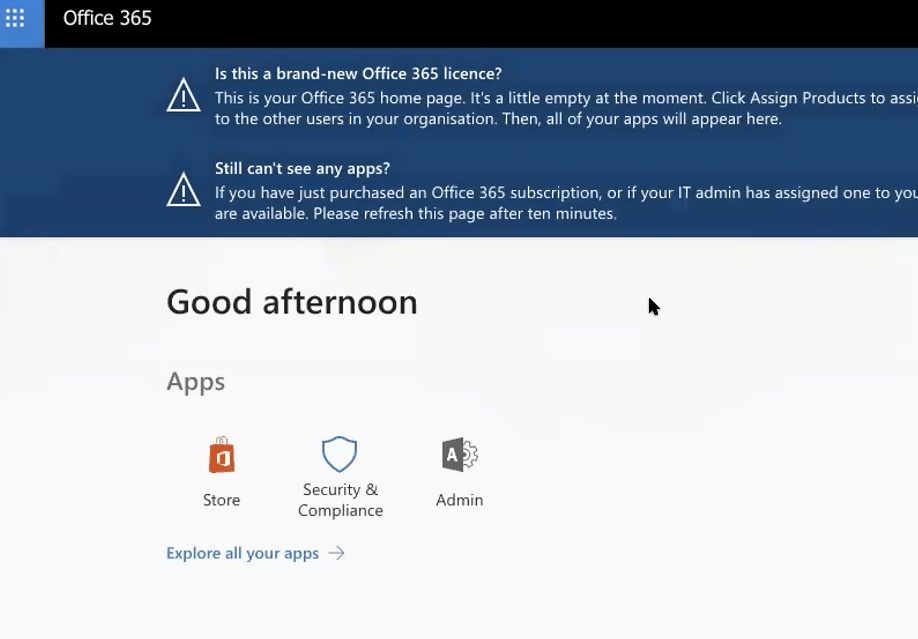
18 . Notice the Office 365 E3 Developer Setup is incomplete. Select the Go to Setup box

19 . On the Microsoft 365 admin center select the Connect a domain you already own radio button and type your AZURE registered Domain
select Next

20 . On the Verify domain page notice there are step-by-step instructions to follow,
- Notice that there are DNS records called TXT name, TXT value and TTL
- These have to be entered in our AZURE DNS service
To do this will require us switching between the Office 365 Admin Console and Microsoft Azure
21 . On the Microsoft Azure Admin Console, select All services, select DNS Zones, in the DNS Zones area select your DNS Zone and select + Record Set

22 . In the Add record set window type in the following:-
- Under Name enter @
- Under Type, select TXT
- Under TTL type 1
- Under TTL unit select Minutes
- Next switch back to your Office 365 environment and copy the following Next to TXT value:

- Next switch back to you Azure Admin Console > under Add record set and paste the copied data from Office365
under the VALUE section

- Select OK

23 . On the Office 365 Admin Console select Verify

24 . On the Add new users page accept the default and at the bottom of the page select Next
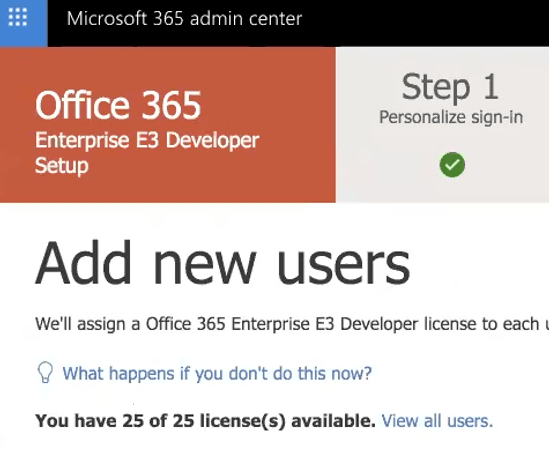

25 . On the Assign licenses to unlicensed users leave all boxes unchecked, Select Next
26 . On the Install your Office apps page select Next

27 . On the Migrate email messages, ensure the Don’t migrate email messages radio button is selected select Next

28 . On the Choose your online services page ensure the checkbox next to Exchange as well as Skype for Business has been selected, Select Next

29 . On the Add DNS Records page add the following:-
- Under MX Records
- CNAME records
30 . Select + Record set On the Add record set page add the following:-
- Under Name enter autodiscover
- Under Type select CNAME
- Under TTL type 1
- Under TTL unit select Hours
- Under Alias type Autodiscover.outlook.com
31 . Select OK

32 . Select + Record set On the Add record set page add the following:-
- Under Name enter sip
- Under Type select CNAME
- Under TTL type 3600
- Under TTL unit select Seconds
- Under Alias type sipdir.online.lync.com
- Select OK

33 . Select + Record set On the Add record set page add the following:-
- Under Name enter lyncdiscover
- Under Type select CNAME
- Under TTL type 1
- Under TTL unit select Hours
- Under Alias type webdir.online.lync.com
- Select OK

34 . Select + Record set On the Add record set page add the following:-
- Under Name enter @
- Under Type select TXT
- Under TTL type 1
- Under TTL unit select Hours
- Switch back to Office 365 and under TXT records select Copy to clipboard

- Switch back to Microsoft Azure to the Add record set page and under VALUE paste the data you have just copied


- Select OK
35 . Select + Record set On the Add record set page add the following:-
- Under Name enter _sip._tls
- Under Type select SRV
- Under TTL type 3600
- Under TTL unit select Seconds
- Under Priority type 100
- Under WEIGHT type 1
- Under PORT type 443
- Under TARGET type sipdir.online.lync.com
- Select OK

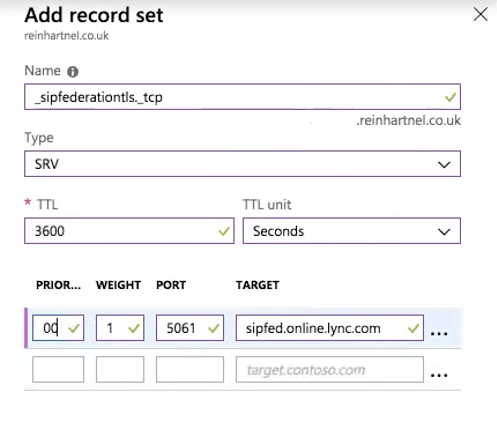
36 . Select + Record set On the Add record set page add the following:-
- Under Name enter _sipfederationtls._tcp
- Under Type select SRV
- Under TTL type 3600
- Under TTL unit type Seconds
- Under Priority type 100
- Under WEIGHT type 1
- Under PORT type 5061
- Under TARGET type sipfed.online.lync.com
- Select OK
37 . Switch back to the Microsoft 365 admin center and select Verify
38 . You should get a You’ve reached the end of setup

Setting up your SAAS VMware Identity Manager and
Connector
- Overview: To deploy the VMware Identity Manager Connector. Pre-reqs: We need to download the VMware identity Manager Connector from the VMware downloads site.
1 . On receiving confirmation of the Tenant details in your email, select the Set Password URL:

2 . On the Change your password Windows type and confirm your new password and then select Change Password
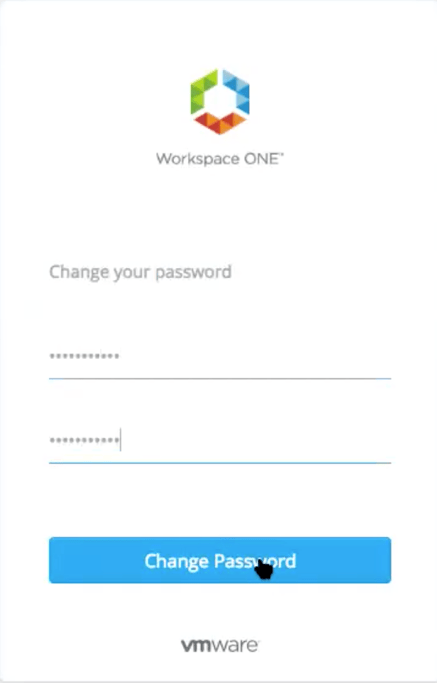
3 . On the Your password has been changed window select Go to Sign in page

4 . On the login page under Username type your username and under Password your password
5 . Select Sign in

6 . On the Terms and Conditions page, select Accept

7 . On the VMware Identity Manager Admin portal, select the Identity & Access Management tab

8 . To the right of the Identity & Access Management page select Setup, you will notice you default to Connectors page , select Add Connector


9 . On the Add a Connector window, next to Connector ID Name type the ID VIDMCON , next select the Generate Activation Code button. In the Connector Activation Code area, SELECT ALL and COPY, select OK

10 . We will now switch to Deploying the VMware Identity Manager Connector
11 . Using your RDP connection Login into your AD server in Azure and downloads the latest version of the VMware identity manager connector.
12 . Once Downloaded go to the Downloads folder and execute the VMware identity Manager Connector installer, when prompted select RUN

13 . On the Welcome to the Installation Wizard for…. window select Next

14 . On License Agreement window select the I accept the terms…. Radio button and select Next

15 . On the Custom Setup page ensure the VMware identity Manager Connector is selected, select Next
16 . On the Destination Folder page select Next

17 . On the Question window select Yes

18 . On the VMware Identity Manager Connector Configuration page change the existing Connector port from Port 443 to 8500 select Next


19 . On the Connector Activation page, next to Activation Code: Paste the copied Code into the available area and next to Admin Password and Confirm Password, type the password of your SAAS tenant. Next to Would you like to activate the Connector now? Select the Yes radio button Select Next
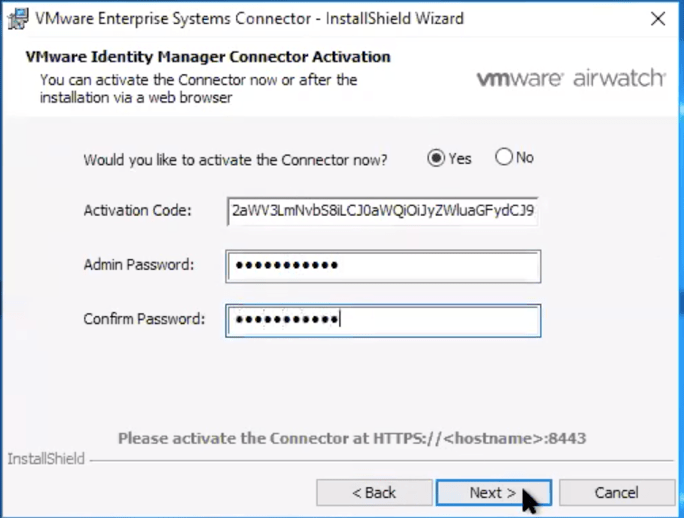


20 . On the VMware Identity Manager Connector Service Account window under User Name, type your domain\vidmservice account and fill in your password, select Next
21 . On the Ready to install the Program select Install. On completion select Finish
Setting UP Directory Sync with VMware Identity Manager

1 . On the Identity & Access Management tab select Manage and select Add Directory

2 . On the Directories page under Add Directory select Active Directory over LDAP/IWA
3 . On the Add Directory Page next to Directory Name type your Azure based AD domain name and select the Active Directory (Integrated Windows Authentication) radio button
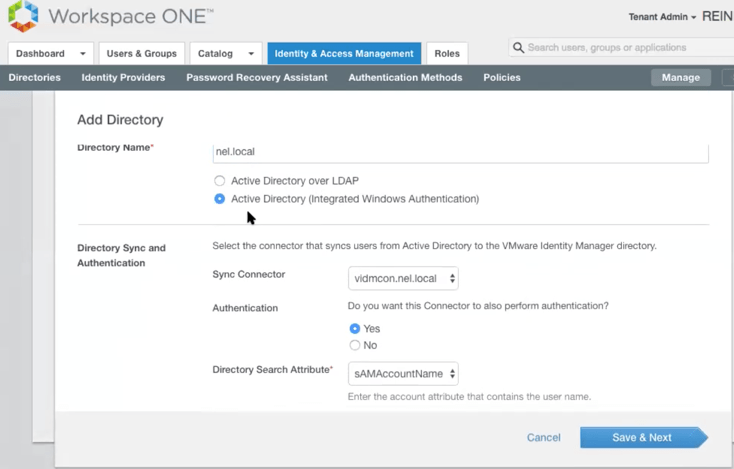
4 . Scroll down to the Bind User Details section, next to Bind User Name type your vidm service account name and next to Bind User Password type the password . Select the Save & Next button



5 . On the Select Domains window ensure your Domain checkbox is selected and select Next

6 . On the Map User Attributes window select Next
7 . On the Select the groups you want to sync page, select Next

8 . On the Specify the users you want to sync under the Specify the user DNs box type the bind path structure for your OU structure. eg. ou=root,dc=nel,dc=local


9 . Select Next
10 . On the Review page, select Sync Directory

11 . Next select the Users & Groups tab to see if your custom AD accounts have synced.

Configuring Outbound Authentication in VMware Identity
Manager
1 . Select the Identity & Access Management Tab, to the right select Setup then select Identity Providers, then select the Built-in IDP


2 . On the Built-in IDP page next to users select your AD domain check box, Do not select System Directory. Next to Network select ALL RANGES checkbox
3 . Next to Connectors in the Add a Connector area select the dropdown for your external connector and then to the bottom of the page select Add Connector

4 . Next to Connector Authentication Methods under Associate Authentication Method, select the checkbox and select Save

5 . To the right of the page select Policies and wait for the Policies page to load. Move your pointer over and select the default_access_policy_set

6 . In the default_access_policy_set page select EDIT

7 . In the Edit Policy page select Configuration, select the first Policy by selecting All RANGES


8 . In the Edit Policy Rule next to then the user may authenticate using Password, select Password (cloud deployment) select SAVE
9 . On the Edit Policy page select Next

10 . In the Summary section select SAVE

11 . You are should now be good to test your AD based user account in the Workspace ONE admin Portal
About the Architect and Author of this information
Stavros Charalambous (Architect)
As a Technical Account Specialist, Stavros helps VMware EUC Mobility customers realize the benefits of their investments with VMware Workspace ONE. Prior to that, Stavros spent almost 15 years in the Telco and Service Provider arena, designing and implementing various systems across the Technology and Information Systems domain. Stavros holds the following certifications: VCP-DW, VCP-CMA, VCP-DTM, VCP-NV, VCP-DCV, MCSE, CCNP, ITIL Practitioner, Certified Scrum Master, Prince2 Foundation; is a Subject Matter Expert in the VCP program and an active member of the VMware Identity Manager Product Area Champion Team. (P.A.C.T)
Reinhart Nel (Author)
Reinhart joined VMware as a VMware Certified Instructor in 2013 with a very strong background on vSphere, Horizon and Microsoft Technologies. His main focus was enabling partners across EMEA to Design and Architect solutions in the EUC space using VMware Horizon with vSphere as the Platform.At present he is part of a Team of Solution Architects that are focused on enabling both internal PSO and SE and VMware Partners on a Global basis called Livefire. His underlying passion to share knowledge and traveling drives Reinhart; Livefire has thus far been the highlight of his career. Moving into the Digital Workspace area Reinhart has developed a passion for Solutions in the Identity Space and is now part of the newly formed VMware Identity Manager Product Area Champion Team. (P.A.C.T) .
Reinhart holds the following VMware certifications: VCP 3, VCP 4, VCP 5, VCP5-DT, VCP6-DCV, VCP6-DT, VCP7-DT VCP5-iaas, VCAP4-DCA
Microsoft Certifions: Microsoft Certified Technology Specialist (Windows Server 2008; Exchange 2007)
Microsoft Certified Systems Engineer (MCSE) (NT4; Windows 2000; Windows 2003)
ITSMF : ITIL Foundations v3













That’s good stuff Stavros and Reinhart, well done both! Very useful.
Thanks for the info, really useful but.. How can I get an “approved MSDN subscriptions with your VMware account” ?
Hi Pablo, I am guessing you mean your own vmware subscription. Submit a Helpnow request and also get your manager approval.
Hi Reinhart,
Sorry but would you plese let me know how a helpnow request should be raised?
Any email or contact details?
Thanks
Amazing job!!
So many thanks for putting this together, this really helps moving forward with our labs and is saving many, many, many … hours of research.
So much detail and very well explained!! I was looking for something like that for a long time!
Thank you very much!!!
Second that, what an amazing guide!
Big thanks to both of you Reinhard & Stavros for the amazing job.