Although announced earlier this year (May) there are still many questions around what VMware and Okta’s partnership announcement means for EUC and Access management.
There are multiple options to implement the integration depending on a customer’s existing investments in both the identity and access management space. The real benefit to the integration is bringing together the two best of breed solutions in both the access management space through Okta and the digital workspace including Unified End-Point Management, Horizon and vIDM delivered through Workspace One.
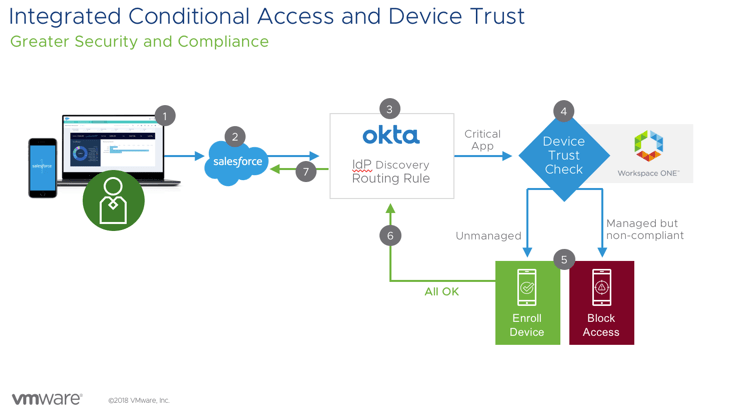
In my humble opinion, among all the ways to implement the integration technologically (See comprehensive guide attached) the strength of this partnership lies in the ability for existing Okta customer’s to leverage the multi-factor authentication such as Mobile Single sign on that Workspace One has to offer. This allows VMware Identity Manager (vIDM) to act as an identity provider to Okta giving administrators the ability to set whether an application that is federated with Okta can leverage authentication methods setup in vIDM. Workspace One Unified End-point Management allows for administrators to deem a device compliant or non-compliant based on certain criteria that can be leverage by vIDM in the authentication process. The compliance status can then be leveraged in conjunction with Okta’s Sign On policies for authentication using vIDM as a third-party identity provider.
To implement the above scenario begin on page 37 of the attached document.
Title of Article is “Workspace ONE as Identity Provider in Okta“
Okta 3rd Party UEM – Workspace ONE v1.1
Setting up a Free Okta Developer account
Rather than using a production environment, I’d highly recommend first simulating such authentication flows using a Free Okta developer account and a test Workspace One tenant. The instructions to do so are below:
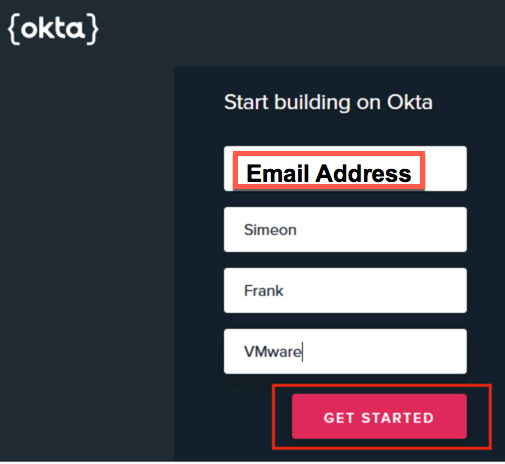
1. Open your choice of browser and browse to https://developer.okta.com
2. Click on Create Free Account
3. Fill the form using a public e-mail address like gmail, hotmail, yahoo. This will later be the admin username for the developer account. Fill in your first and last name and company.
4. Select GET STARTED
5. Now Check you e-mail and copy the temporary password and click on the link in the e-mail
6. Now type in the e-mail that you used as your username and the temporary password. Fill in the form to set a new password, a security question & answer, and select an image.
7. Notice once you are logged in you will have a unique DEV tenant. You have now registered successfully for a developer account.